Introduction to the Message Data Model
Overview
The Message Data Model (MDM), or MDM, is one of the core building blocks of the Sublime system. It is a structured data model representation of an email message designed to make rule writing predictable, easy, and intuitive.
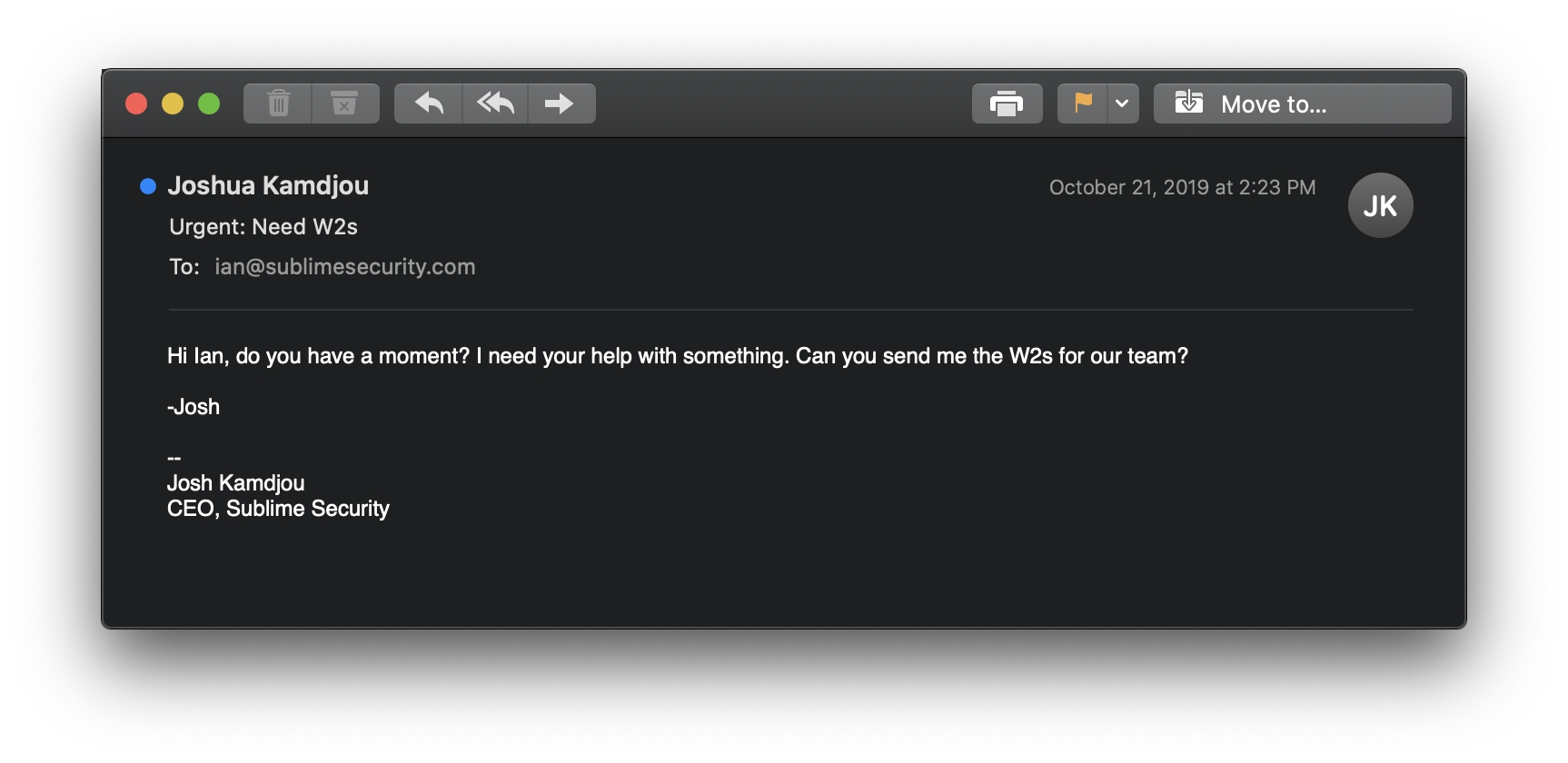
Let's take a look at how a raw email message gets transformed into an MDM.
First, download the message here.
View the contents of the raw message:
head impersonation.eml
Output:
Delivered-To: [email protected]
Received: by 2002:a2e:5419:0:0:0:0:0 with SMTP id i25csp4721902ljb;
Mon, 21 Oct 2019 11:23:39 -0700 (PDT)
X-Received: by 2002:a05:6e02:a:: with SMTP id h10mr3524960ilr.254.1571682219618;
Mon, 21 Oct 2019 11:23:39 -0700 (PDT)
ARC-Seal: i=1; a=rsa-sha256; t=1571682219; cv=none;
d=google.com; s=arc-20160816;
b=UjFMxEI17M6u7hd/V3tM+q/qAYJeKUX6+wZaFWZrXAi/H8RWsiUcBcnPzc8mx1c8d4
q6YIqczF3TEs6wfbbuAgHbel8oAYegOchVgiv0NTgmQsOQ2rzxC2vzyc2ynBdusQUGsv
M1TPSJcRHOeimJr5vJA+LDrkKoBhq+Hd8CAqfLycaqnVTK9gWsdP0l2B3phWMGw7a91X
View the sender of the email:
grep 'From:' impersonation.eml
Output:
From: Joshua Kamdjou <[email protected]>
Create a Message Data Model
Now, let's create an MDM from our raw EML.
Install the Sublime CLI:
pip3 install sublime-cli
Now, let's create the MDM:
sublime create -i impersonation.eml
Output:
Output saved to impersonation.mdm
The MDM is stored as a JSON object, and organizes the message into distinct hierarchical objects that make it easy to find what you're looking for in a message. For example, to view the sender of the message, just output the top-level sender object using an MQL query (more on that later):
sublime analyze -i impersonation.mdm -q sender
Output:
╔═══════════════════════════╗
║ Results ║
╚═══════════════════════════╝
File Name: impersonation.mdm
Total Rules: 0
Total Queries: 1
QUERIES
- Query 1
Result: {
"display_name": "Joshua Kamdjou",
"email": {
"email": "[email protected]",
"local_part": "joshkamdjou90",
"domain": {
"domain": "gmail.com",
"root_domain": "gmail.com",
"sld": "gmail",
"tld": "com",
"valid": true
}
}
}
Instead of an unformatted string, the sender object is tokenized and designed to make rule writing easy!
You can view the other objects of the MDM anytime using the Message Data Model (MDM) reference.
In the next tutorial, we'll learn how to use this information to write a rule for this impersonation attack.
Updated about 3 years ago